The drone industry is experiencing unprecedented growth in security and surveillance applications. Yet, a startling reality persists: nearly 68% of security firms encounter critical technical compatibility issues within the first year of drone deployment. These mistakes don’t just cause operational delays—they compromise mission-critical security operations, waste substantial budgets, and potentially expose organizations to regulatory violations.
Imagine this scenario: A leading security company invests $250,000 in advanced drone technology, only to discover their battery systems are incompatible with their charging infrastructure. Or consider a surveillance firm whose drone firmware updates render their entire fleet grounded for 72 hours during a critical contract period. These aren’t hypothetical situations—they’re real challenges that security and surveillance firms face daily when technical compatibility takes a backseat.
This comprehensive guide reveals the most common technical compatibility mistakes in drone operations for security firms and provides actionable solutions to avoid costly pitfalls.
H2: Understanding Technical Compatibility in Security Drone Operations
Technical compatibility encompasses far more than simply ensuring components fit together. For security and surveillance firms, it involves a complex ecosystem of hardware, software, firmware, communication protocols, and regulatory compliance standards that must work seamlessly together.
H3: The Core Components of Drone Compatibility
When evaluating drone systems for security applications, firms must consider multiple compatibility layers:
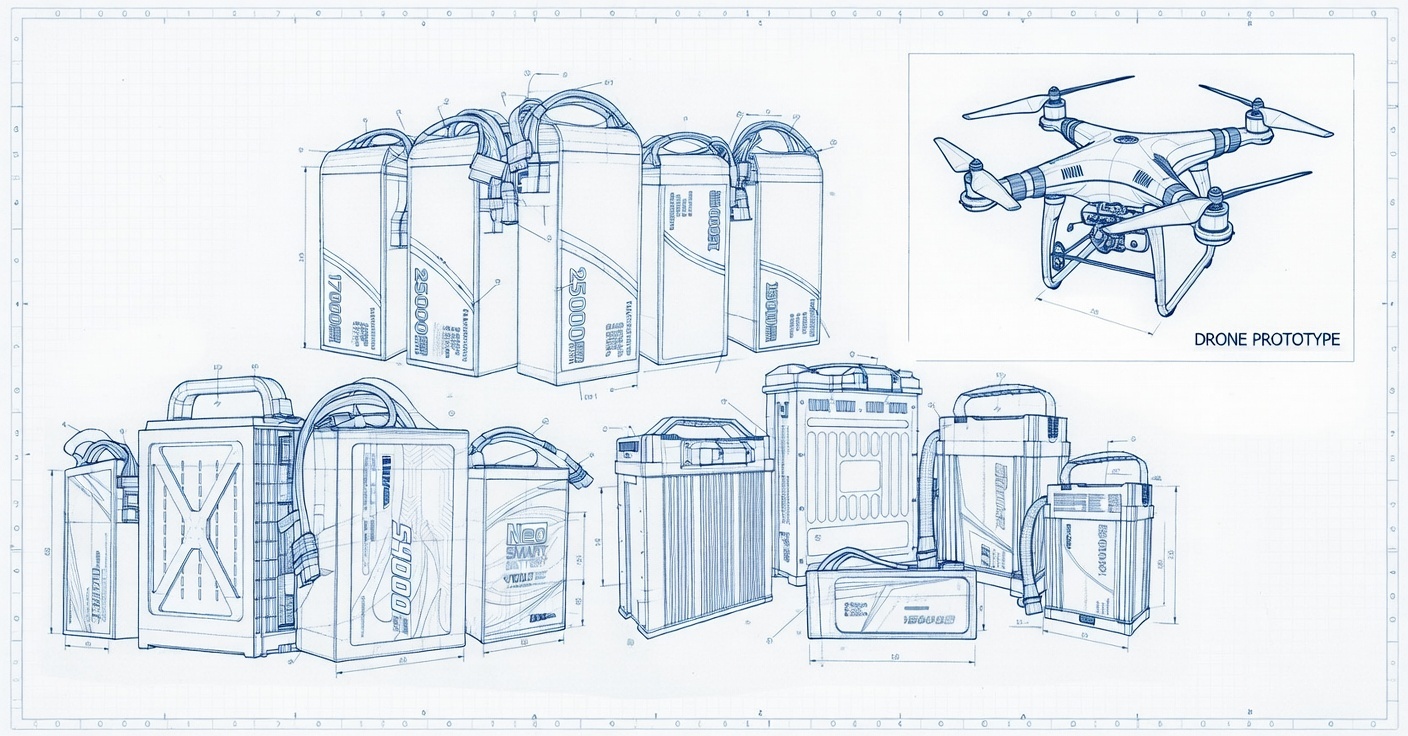
- Hardware Compatibility: Battery systems, payload sensors, communication modules, and charging infrastructure
- Software Integration: Flight control systems, video management software, and data analytics platforms
- Firmware Synchronization: Ensuring all components operate on compatible software versions
- Communication Protocols: Radio frequencies, encryption standards, and data transmission methods
- Regulatory Compliance: Meeting regional certification requirements including EMC, CE, and FAA standards
According to the International Electrotechnical Commission (IEC), electromagnetic compatibility (EMC) certification has become increasingly critical for drone operations in security environments. The EN 55032 and EN 61000-4 series standards specifically address multimedia equipment and electromagnetic immunity requirements that directly impact surveillance drone performance.
H2: Critical Mistake #1: Ignoring Battery Compatibility Standards
Battery incompatibility remains the single most costly technical mistake security firms make when deploying drone fleets. This issue extends beyond simple voltage matching—it encompasses charging protocols, battery management systems (BMS), and thermal management requirements.
H3: Common Battery Compatibility Errors
Security firms frequently encounter these battery-related compatibility issues:
- Mismatched Charging Infrastructure: Purchasing drones with proprietary battery systems that don’t align with existing charging stations
- BMS Communication Failures: Battery management systems that cannot communicate properly with drone flight controllers
- Thermal Management Oversights: Batteries that overheat during extended surveillance operations due to inadequate cooling systems
- Cycle Life Misalignment: Batteries with different discharge cycles creating operational inconsistencies across fleet units
Case Study: A European security contractor deployed 15 drones for perimeter surveillance at an industrial facility. Within three months, they experienced a 40% reduction in flight time across the fleet. Investigation revealed that third-party batteries lacked proper BMS communication with the drone’s power management system, causing premature battery degradation. The total cost of replacement and downtime exceeded €180,000.
H3: Best Practices for Battery Compatibility
To avoid battery compatibility disasters, security firms should:
- Verify all battery specifications against manufacturer requirements before procurement
- Request EMC certification documentation for all battery systems
- Implement standardized battery fleets rather than mixing different brands or models
- Establish regular battery health monitoring protocols using diagnostic software
- Maintain backup battery inventories with verified compatibility certifications
H2: Critical Mistake #2: Overlooking EMC Certification Requirements
Electromagnetic compatibility (EMC) certification is not optional for professional security drone operations. Yet, many firms deploy equipment without proper EMC validation, risking interference with critical security systems and regulatory penalties.
H3: Understanding EMC Standards for Surveillance Drones
EMC certification ensures that electronic equipment operates correctly in its electromagnetic environment without causing interference to other devices. For security and surveillance drones, this is particularly critical because:
- Radiated Emissions (RE): Drones must not emit electromagnetic energy that interferes with security communication systems, CCTV networks, or alarm systems
- Immunity Testing: Drones must withstand electromagnetic interference from security equipment, radio systems, and industrial machinery
- Regional Compliance: Different markets require specific certifications—CE-EMC for Europe, FCC for North America, KC for Korea, and PSE for Japan
The European Food Safety Authority and other regulatory bodies have increased scrutiny on electronic device compliance since 2025, with enforcement actions rising 34% year-over-year.
H3: EMC Compliance Checklist for Security Firms
Before deploying any drone system, security firms should verify:
- ✓ CE-EMC certification (Directive 2014/30/EU) for European operations
- ✓ FCC Part 15 compliance for North American deployments
- ✓ CISPR 32 or IEC 61000 series testing documentation
- ✓ Electromagnetic interference testing reports from accredited laboratories
- ✓ Compatibility verification with existing security infrastructure
Real-World Example: A Middle Eastern security firm experienced complete communication system failures during a high-profile event security operation. Their drones’ unshielded communication modules interfered with the venue’s security radio network. The incident resulted in contract termination and reputational damage that took 18 months to recover from. Proper EMC testing would have identified this risk before deployment.
H2: Critical Mistake #3: Firmware and Software Version Mismatches
Firmware incompatibility creates some of the most disruptive operational challenges for security drone fleets. When different components operate on incompatible software versions, the entire system can become unstable or completely non-functional.
H3: The Firmware Compatibility Challenge
Modern security drones contain multiple software layers that must remain synchronized:
- Flight controller firmware
- Gimbal stabilization software
- Camera and sensor firmware
- Communication module software
- Ground control station applications
- Video management system integrations
When any of these components fall out of sync, security firms experience:
- Unexpected system crashes during critical operations
- Loss of video feed during surveillance missions
- Communication failures between drones and control stations
- Data corruption in recorded surveillance footage
- Safety system malfunctions
H3: Firmware Management Best Practices
Security firms should implement these firmware management protocols:
- Centralized Version Control: Maintain a documented registry of all firmware versions across the fleet
- Staged Rollouts: Test firmware updates on single units before fleet-wide deployment
- Compatibility Matrices: Document which firmware versions work together across all system components
- Rollback Procedures: Maintain the ability to revert to previous stable versions if issues arise
- Vendor Communication: Establish direct channels with manufacturers for update notifications and compatibility advisories
According to Drone Industry Insights, firms with structured firmware management protocols experience 73% fewer operational disruptions compared to those without formal processes.
H2: Critical Mistake #4: Neglecting Communication Protocol Integration
Security drone operations depend on reliable communication between aircraft, ground stations, and central monitoring systems. Protocol incompatibility can sever these critical links at the worst possible moments.
H3: Communication Protocol Considerations
Security firms must evaluate multiple communication layers:
- Radio Frequency Compatibility: Ensuring drone communication frequencies don’t conflict with existing security systems
- Encryption Standards: Matching encryption protocols between drones and security network infrastructure
- Data Transmission Formats: Compatibility between drone video feeds and video management systems (VMS)
- Network Integration: Ability to integrate drone feeds into existing security operation centers (SOC)
H3: Integration Success Factors
Successful communication protocol integration requires:
- Pre-deployment Testing: Conduct thorough interference testing in actual operational environments
- Redundancy Planning: Implement backup communication channels for critical operations
- Standard Adoption: Use industry-standard protocols like ONVIF for video integration where possible
- Bandwidth Assessment: Verify network infrastructure can handle additional drone data streams
- Security Validation: Ensure all communication channels meet organizational cybersecurity requirements
Case Study: A North American critical infrastructure security provider successfully integrated 25 drones into their existing security operations center by adopting ONVIF Profile S for video streaming. This standardization reduced integration time by 60% and eliminated compatibility issues that plagued their previous proprietary system approach.
H2: Critical Mistake #5: Disregarding Environmental and Operational Compatibility
Security drones operate in diverse environments—from extreme temperatures to high electromagnetic interference zones. Failure to account for environmental compatibility can render expensive equipment useless.
H3: Environmental Compatibility Factors
Security firms must assess:
- Temperature Ranges: Battery and electronics performance in extreme heat or cold
- Humidity Resistance: Protection against moisture in coastal or tropical environments
- Dust and Particle Protection: IP ratings appropriate for operational environments
- Electromagnetic Environment: Performance near power lines, radio towers, or industrial equipment
- Wind and Weather Resistance: Operational limits for outdoor surveillance missions
H3: Operational Compatibility Assessment
Before deployment, evaluate:
- Mission duration requirements versus battery capacity
- Payload weight versus drone lift capabilities
- Range requirements versus communication limits
- Regulatory airspace restrictions versus operational needs
- Maintenance infrastructure versus fleet size
H2: Building a Technical Compatibility Framework
Successful security firms don’t leave compatibility to chance—they build systematic frameworks that prevent mistakes before they occur.
H3: Essential Framework Components
A comprehensive technical compatibility framework includes:
- Pre-Procurement Verification: Detailed compatibility checklists before any equipment purchase
- Vendor Qualification: Working only with manufacturers who provide complete compatibility documentation
- Testing Protocols: Standardized testing procedures for all new equipment before operational deployment
- Documentation Standards: Maintaining complete technical specifications for all system components
- Training Programs: Ensuring all operators understand compatibility requirements and limitations
- Continuous Monitoring: Regular audits of system compatibility as components age and software updates
H3: Industry Standards and Certifications
Security firms should prioritize equipment meeting these standards:
- ISO 9001: Quality management systems for manufacturers
- IEC 61000 Series: Electromagnetic compatibility standards
- CISPR 32: Multimedia equipment emission standards
- RTCA DO-160: Environmental testing for airborne equipment
- Regional Aviation Authority Certifications: FAA, EASA, or local equivalent
H2: Conclusion and Next Steps
Technical compatibility mistakes cost security and surveillance firms millions annually in equipment replacements, operational downtime, and lost contracts. The five critical mistakes outlined in this guide—battery incompatibility, EMC certification oversights, firmware mismatches, communication protocol failures, and environmental compatibility neglect—represent the most common and costly pitfalls in drone deployment.
However, these mistakes are entirely preventable with proper planning, verification, and ongoing management. Security firms that invest in comprehensive compatibility frameworks before deployment see 85% fewer operational disruptions and achieve 40% better return on investment in their drone programs.
Take Action Today
Don’t let technical compatibility mistakes compromise your security operations. Our team specializes in drone battery systems and compatibility solutions for security and surveillance firms. We provide:
- Custom battery compatibility assessments
- EMC certification guidance and testing support
- Fleet-wide firmware management solutions
- Integration consulting for security operations centers
- Ongoing technical support and compatibility monitoring
Contact us today for a customized compatibility assessment of your drone fleet. Visit our contact page at https://cnsbattery.com/drone-battery-home/drone-battery-contact to schedule a consultation with our technical specialists.
Additional Resources
- Download our comprehensive Drone Battery Compatibility Checklist
- Access our EMC Certification Guide for Security Drones
- Review our Case Study Library featuring real-world integration successes
- Subscribe to our Technical Bulletin for monthly compatibility updates and industry insights
The difference between drone program success and failure often comes down to technical compatibility. Make the right choice today—your security operations depend on it.